Many customers thinking about AI governance for the first time arrive with similar assumptions about their existing IdP strategy. What they don’t realize at first is how these assumptions are holding them back.
First, that identity is sufficient. These customers are treating AI agents like any other software – grant access, applying existing roles and access controls, and carry on as usual. But AI isn’t like any other software. They’re operating as autonomous digital actors, behaving almost like employees except without human judgement.
The second is that implementing AI governance means disrupting their existing identity set up. This assumption is false – the right AI governance layer connects seamlessly with your existing identity provider and works alongside your implementation.
Finally, they believe that AI governance and identity management are somehow incompatible, siloed security stacks that don’t share the same foundation. In reality, they’re complementary and work together!
Let’s explore the 10 most common questions customers ask us about identity and AI governance
What’s the difference between an identity provider and AI governance?
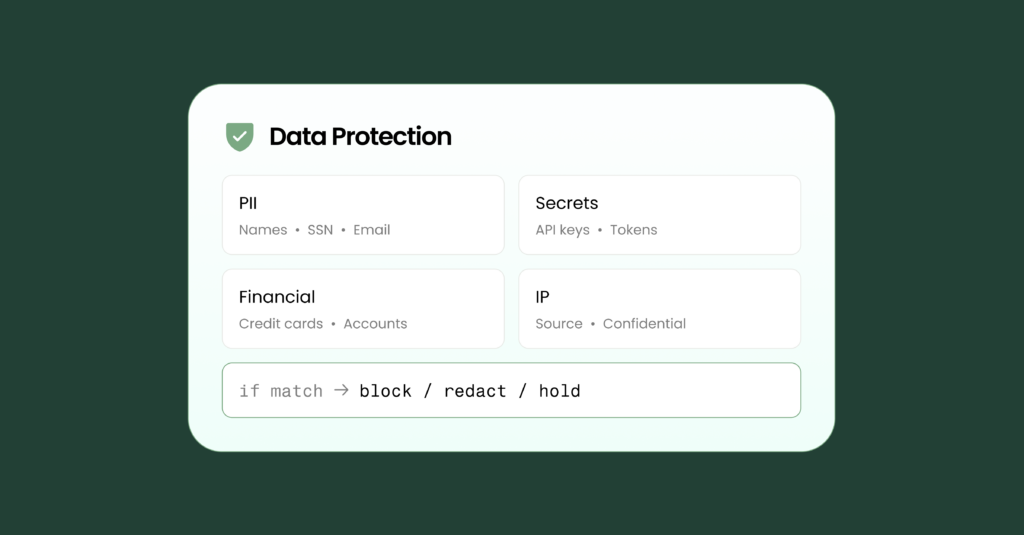
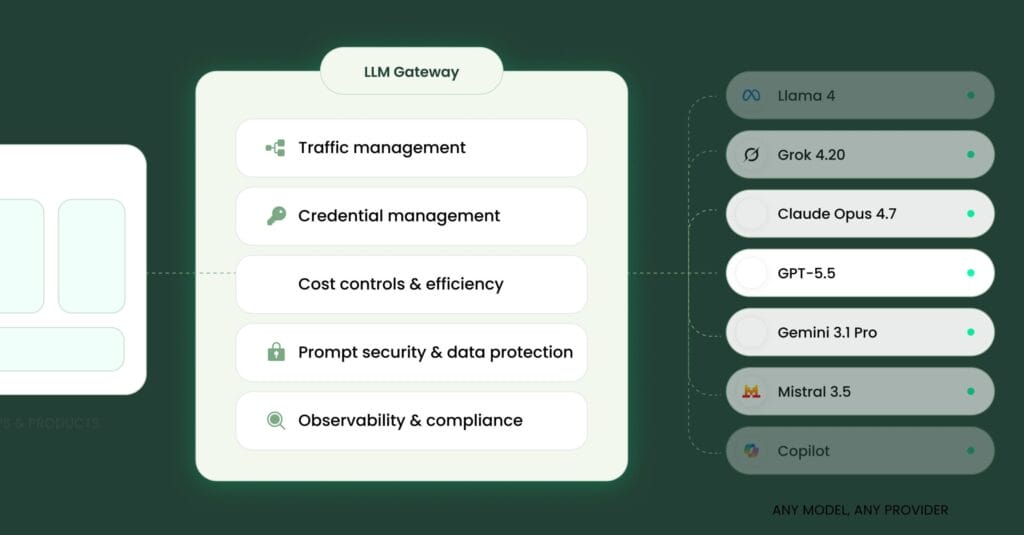
Your IdP controls who can authenticate and what resources they are authorized to access. AI governance controls what an AI agent actually does once it has access. This includes the tool calls it makes, the data it reads or writes, the decisions it makes, and whether any of those actions require human-in-the-loop review.
Does Barndoor replace my identity provider?
No! Barndoor integrates right into your existing identity provider: Okta, Microsoft Entra ID, Ping Identity, or any OIDC and SAML 2.o compatible IdP, and builds on top of it for your agents. There’s no disruption to what you have today – your SSO and group structures. Barndoor adds a new agent governance layer, without interrupting your current identity and access management stack.
Can my existing RBAC policies apply to AI agents?
Role-based access control determines what an agent is authorized to access at the resource level. But RBAC alone cannot monitor and enforce behavioral policies for example “this agent must not be able to make a delete action without human approval” or “this agent may only read customer data, not write it.” Barndoor supports your RBAC with agent enforcement.
What identity providers does Barndoor support?
Barndoor works with any identity provider that supports OIDC or SAML 2.0. This includes Okta, Microsoft Entra ID (formerly Azure AD), Ping Identity, Google Workspace, Auth0, and OneLogin, among others.
Can I use Okta with Barndoor?
Yes. Barndoor supports Okta via OIDC or SAML 2.0. Once connected, all users in your organization authenticate via Okta SSO, and user roles are automatically provisioned in Barndoor based on your existing Okta group structure.
Can I use Microsoft Entra ID with Barndoor?
Yes. Barndoor supports Microsoft Entra ID (formerly Azure AD) via OIDC or SAML 2.0. Your existing group structures and role assignments flow directly into Barndoor without requiring a separate configuration.
How does Barndoor handle user offboarding?
When an employee or end user leaves your organization, has changed groups/roles, or is removed from your IdP, they lose access to Barndoor on their next login. Removing a user from your IdP means they can no longer authenticate via SSO, revoking their access.
Why isn’t SSO enough for AI governance?
SSO determines which human identities can access your applications. Agentic governance gives you visibility and control over what the AI is doing, which apps, tools, and data it’s trying to access. Something to keep in mind as well is that many applications your employees are using could be sitting outside of your SSO perimeter. In fact, many applications – third party, legacy, developer tools, and external APIs are not covered by your SSO and therefore, not connected to your IdP in the first place. For human employees, this gap can be addressed through credential management. But for AI agents, this gets trickier. SSO covers who initiated an action; agentic governance addresses what the AI did.
Does Barndoor require admin-level access to my IdP?
Connecting Barndoor requires standard OIDC OAuth credentials from your IdP: the Issuer URL, client ID, and client secret. No admin API access is needed. Barndoor’s setup guide walks through what to collect from your IdP.
How long does IdP integration take?
For most organizations, connecting Barndoor to an existing Okta or Entra ID instance takes a few minutes. Your IT admin will need your IdP’s OIDC URL or SAML metadata, and Barndoor’s setup guide walks through the rest.
Book a Barndoor demo
Barndoor integrates with your IdP and gives you the governance layer that strengthens your overall security posture for both humans and agents. Check out Barndoor IdP setup documentation for details, or schedule a demo to experience what complete agentic oversight looks like.